Standard antivirus is no longer sufficient. A single compromised laptop or workstation can provide a gateway for ransomware to paralyze your entire organization. Small-to-medium-sized businesses (SMBs) are increasingly targeted because they often lack the 24/7 monitoring needed to detect sophisticated lateral movement within their networks. Relying on reactive security measures puts your data, reputation, and financial stability at significant risk. Let’s talk about how endpoint detection and response mitigates these risks.
Imagine a partnership where your provider makes the most money when your business is at a standstill. It may sound backward, but this is the reality of the traditional break-fix model. When your server crashes or your network lags, their billable hours start climbing. This creates a fundamental conflict of interest: Why would a vendor work to prevent the very problems that fuel their revenue?
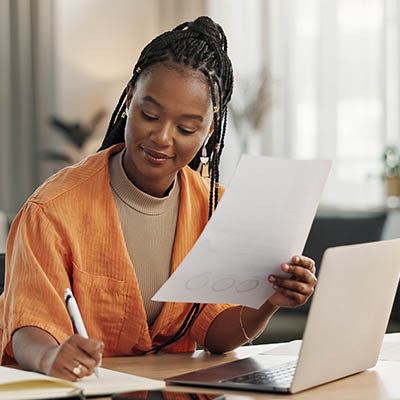
The traditional help desk addresses technology that’s already broken, which doesn’t help you much when you factor in the costs of lost opportunities and productivity. With us on your side, however, you can leverage more proactive solutions that make tech fixes feel more like a high-tech production line. Instead of waiting for the phone call that something’s wrong, we use Remote Monitoring and Management (RMM) tools to find and fix bugs before they ever become a problem for your employees.
Hardware procurement is often the invisible ceiling that halts your company’s growth. If you’re in a time of rapid expansion, the traditional way of buying technology—researching specs, waiting for shipping, and manual setup—is going to hold you back from taking meaningful action. In other words, you don’t have the luxury of waiting three weeks; you need to make things happen now.
Who at your business has the organizational knowledge to keep your technology up and running? The problem with small business IT is that the information on how to keep that technology in proper working order is siloed in one particular individual’s head, whether that’s you as the business owner or one particularly tech-savvy person on your staff. By allowing this information to remain undocumented, you’re actively putting your business at risk by artificially creating a single point of failure.
Sometimes, it can seem that business technology is a bit like the weather—just wait five minutes, and it’ll change. However, for a small business, those changes can sometimes feel less like a refreshing breeze and more like a localized thunderstorm inside your server room. Of course, when you’re busy running a business, you shouldn’t have to be an amateur sleuth to figure out why your Wi-Fi is acting up. Here are a few common technology oddities your team might encounter, along with how a proactive partner keeps the “glitches” at bay.
If you think your business is immune to the dangers of cybersecurity attacks, think again. Cybercriminals don’t discriminate, and they’ll attack you just as readily as a larger enterprise simply due to your weaker network security. If you want to keep your business from suffering a cybersecurity attack needlessly, we’ve got just the thing for you.
Most stories you consume will follow the format of introduction, rising action, conflict, falling action, and resolution. The tense parts of the story, the rising action and conflict, are what drive it forward, and they’re also what make things interesting along the way. That said, you can’t run your business like a story, and you can’t run your IT in this way either.
It’s easy to fall into the trap of thinking that IT is more of a cost than a savings mechanism. But in reality, IT is a powerful tool that can help your business eliminate unnecessary expenses, improve operations, and stop problems in their tracks before they even exist. This approach, proactive IT, has many benefits, all of which save you money.
This time of year is rife with traditions, from the foods we eat to the rituals we follow… even the songs we sing. We wanted to share a little reworking of a classic carol that exemplifies our commitment to the businesses we work with in the spirit of the season.